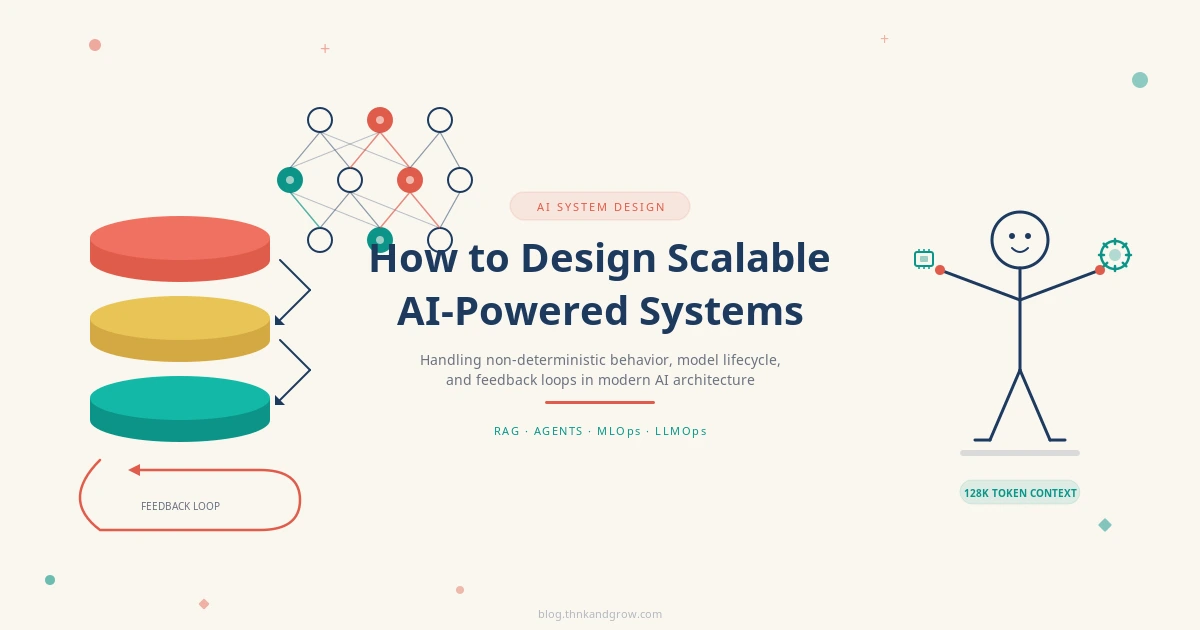
How to Design Scalable AI-Powered Systems in 2026
Building AI-powered systems in 2026 looks nothing like traditional software architecture — and the gaps…
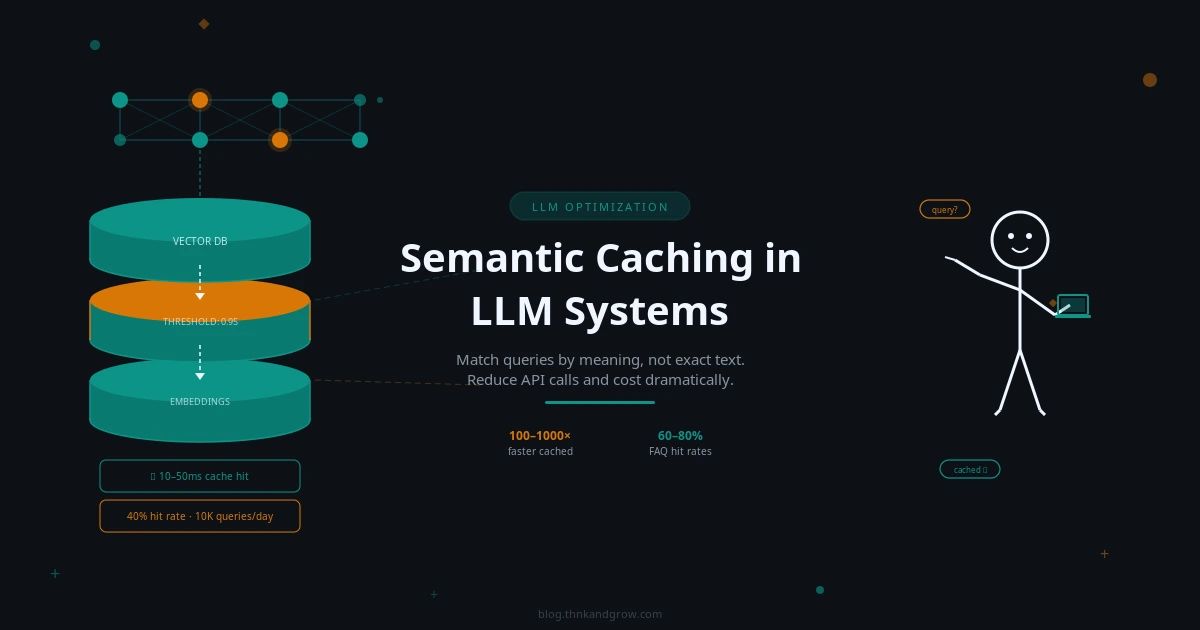
Semantic Caching in LLM Systems: A Beginner’s Guide
Paying for the same LLM response twice is money you don't have to spend. This…
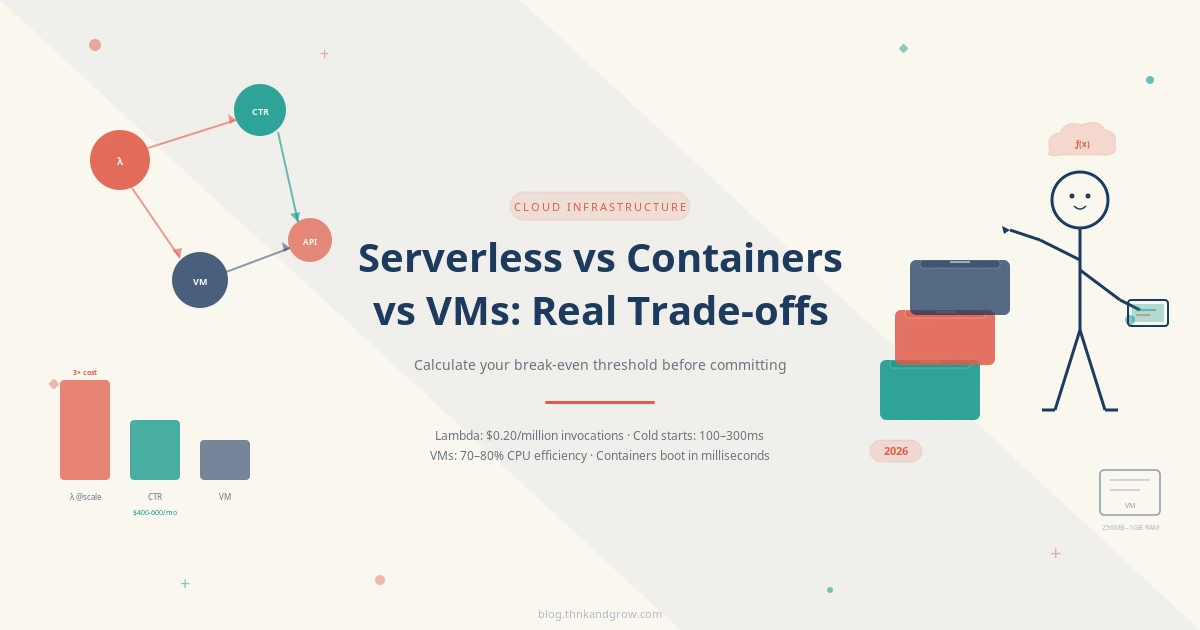
Serverless vs Containers vs VMs: Real Trade-offs in 2026
Serverless isn't always cheaper, containers aren't always portable enough, and VMs aren't dead — the…
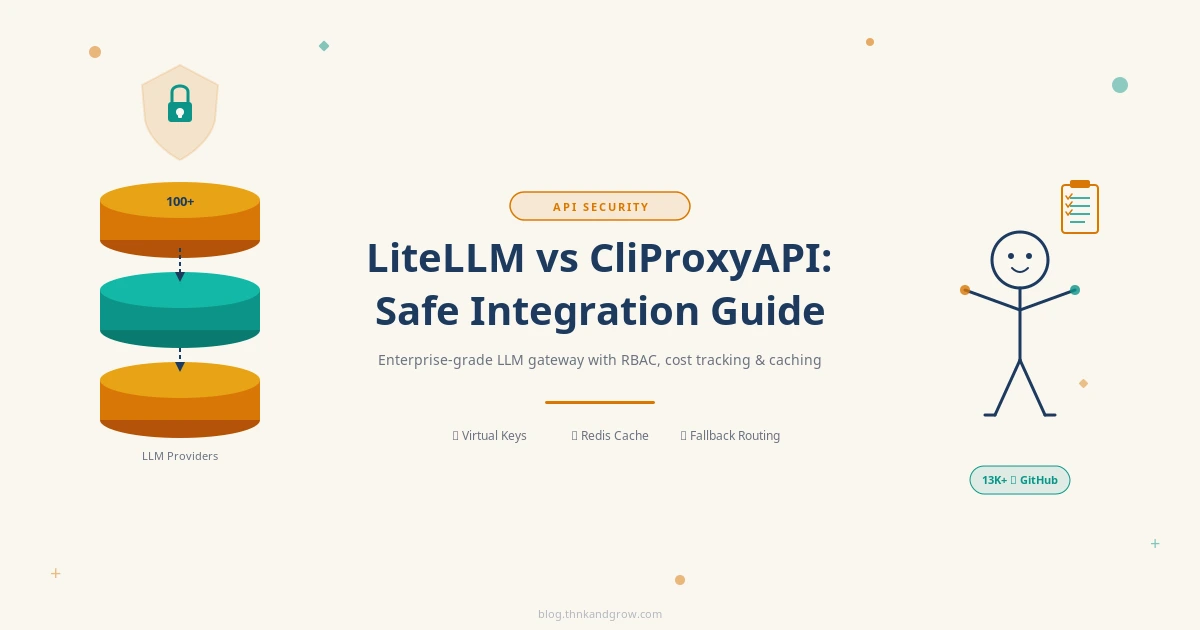
LiteLLM vs CliProxyAPI: Safe Integration Guide 2026
Combining LiteLLM with CliProxyAPI sounds powerful — but done wrong, it can expose your API…
DSPy + LiteLLM + ChatGPT: Build Smarter AI Pipelines in 2026
Stop wrestling with brittle prompts and hardcoded model dependencies. In this guide, you'll learn how…
System Design Numbers Every Engineer Must Know in 2026
Most engineers guess at scale — the best ones calculate it. In this post, you'll…
Nitro App Hooks in NuxtJS: A Complete Guide
Ever wished you could tap into NuxtJS's server lifecycle without touching the core? This guide…
AI Limitations Uncovered: What Chatbots Can’t Really Do
Think your AI chatbot can just "click the link" you sent it? Think again. This…
Top AI Productivity Tools Reshaping Tech in 2025
AI tools in 2025 aren't experiments anymore — they're reshaping how real engineering gets done.…
Plan with Opus, Code with Sonnet: The opusplan Guide
Learn how opusplan uses Claude Opus for smart task planning and Claude Sonnet for coding…